“How dangerous is this user?”
It’s a simple question, and you’d expect a quick and simple answer. A few seconds, maybe. Instead, it turns into a half-hour deep dive through IAM policies, roles assigned to groups, access logs, all with that nagging suspicion we’re still missing something important.
This is a failure of interpretation. And it’s a time sink that’s dragging down GRC teams trying to manage identity risk at any scale.
There has to be a better way...
The Hidden Cost of “Just Checking Access”
In practice, if an engineer spots a potentially over-privileged user in AWS, to validate the risk, they have to pull IAM roles and group memberships, expand attached policies, scan audit logs for usage, cross-check services accessed, look for inherited permissions, and try to work out what the user actually needs. That’s if they’re experienced and have unlimited free time.
Multiply that across hundreds of identities, thousands of permissions, multiple clouds, SaaS applications, service accounts, non-human identities, and AI agents.
Control starts to slip not because the data isn’t there, but because clarity and turning that data into a decision takes too long.
The Data Exists. The Answers Don’t.
AWS, Azure, and GCP all provide IAM policies and roles, activity logs, and access analysis tooling, but they don’t answer the basic questions that actually matter most:
- What can this identity actually do?
- Do they ever use this access?
- What happens if they’re compromised?
Sure, tools like AWS IAM Access Analyzer help surface issues, but they still require interpretation, and invariably comes with cost and noise. They can show potential risk, with some serious investigation, but not clear outcomes.
This is operational friction with real consequences.
Identity Risk Has Outgrown The Model
Access used to be a whole lot simpler.
Now it spans multi-cloud environments (AWS, Azure, GCP), SaaS platforms (GitHub, Salesforce, Snowflake), automation pipelines (CI/CD, scripts), non-human identities (service accounts, bots), and AI agents acting on behalf of users. Each system looks manageable on its own, but together, they create something far more complex. A distributed, invisible attack surface.
Talking to our prospects and clients, we realized that most tools still expect humans to manually piece that picture together. We knew there had to be a better way.
Security teams don’t necessarily lack visibility. They lack time, context, and clear, actionable answers.
When decisions depend on reading policy documents, interpreting logs, and inferring intent, everything slows down. And when things slow down, access reviews become rushed, over-privilege persists, orphaned accounts remain active, and risk accumulates quietly.
Not because teams aren’t capable, but because the process doesn’t scale.
Enter AI-Powered Security
This is where we saw a real opportunity to feed access intelligence to AI-functionality in a truly valuable way. Instead of navigating dashboards, writing queries, and stitching together context, what if we could just ask a question?
- “How destructive can this user be?”
- “Who has unused admin access in AWS?”
- “Show me orphaned accounts across SaaS apps”
What if AI could give a plain-English explanation of risk, a breakdown of what actions are possible, context across cloud and SaaS, and immediate remediation options?
Well, now it can.
And so, in our latest release, this is what AI-powered security actually looks like in practice. Not just automation or a bolt-on chatbot. Clear interpretation at speed.
From Complexity to Decisions
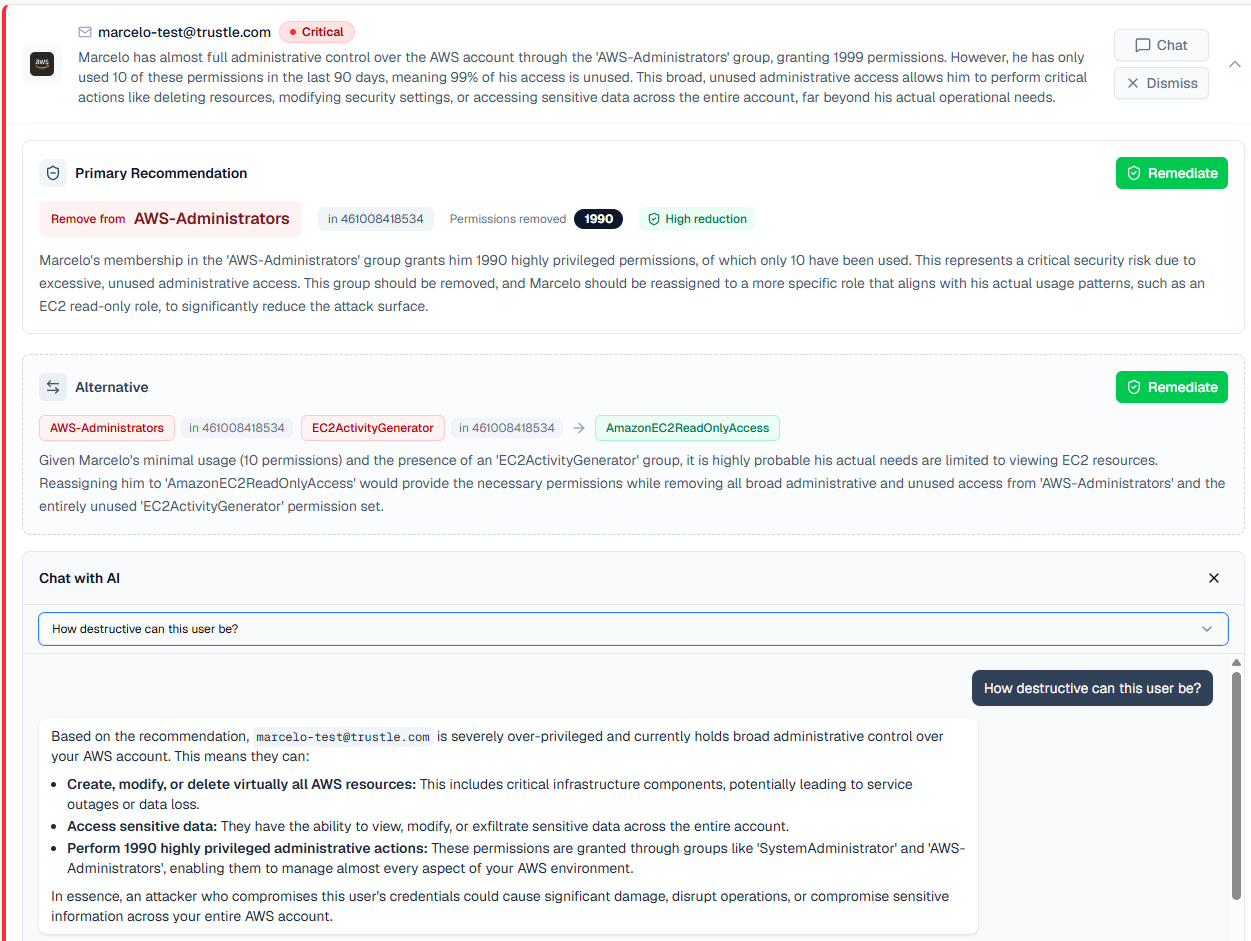
If a user sits in an AWS Administrators group with nearly 2,000 permissions, traditionally, we’d spend 30 minutes working out what those permissions allow, whether they’re used, and what the real risk is.
With our AI-powered approach, you get:
- Clear risk: Only a small fraction of permissions are used
- Impact: Full administrative control, including destructive actions
- Recommendation: Revoke admin role, grant these 3 read-only roles
- Action: Click to remediate immediately
The difference isn’t more data or just another AI bolt on. It’s faster, clearer decisions.
What This Changes For The SOC
This is more than a usability improvement. It changes how teams operate.
From Investigation to Instant Understanding
No more stitching together logs, policies, and guesswork.
You get context, risk, and action in one place.
From Static Access to Time-Bound Access
Standing privilege is replaced with:
- Just-in-time access
- Expiring permissions
- Policy-driven approvals
From Periodic Reviews to Continuous Control
Unused access is identified and removed automatically.
Least privilege becomes measurable and provable.
From Tools to Workflows
Access decisions happen inside:
- Slack
- Microsoft Teams
- Automated pipelines
Security becomes part of daily work. Not a bottleneck.
Why Clarity Matters More Than Ever
Excessive permissions are reported as one of the top three fastest-growing risks. IBM explicitly links “poor access controls” to increased risk of sensitive data compromise, where 99% of cloud identities are over-privileged, with identity issues accounted for 44% of cloud security alerts. Over-privileged access is scaling faster than controls, permissions are growing faster than governance, and identity risk is compounding, not just increasing.
AI agents and automation are accelerating the problem. We now have identities acting independently, permissions chaining across systems, and access that lacks clear ownership This creates invisible trust chains, where one system’s access quietly enables another.
And we can’t manage that with dashboards alone. We need context, interpretation, and immediate action. Delivered without delay.
For years, identity security has focused on visibility. But visibility without understanding is just noise. The real shift with AI-powered security is in moving from analyzing access to interrogating your risk. Once risk is clear, action follows naturally.
If answering one IAM question still takes 30 minutes, the problem isn’t our tooling. It’s how much work it takes to understand what that tooling is telling us. AI-powered security compresses that gap, turning complexity into something far more useful:
Decisions we can trust, and act on immediately.
In about 30 minutes, map every entitlement across users, agents, and SaaS, uncover unused access, and surface wasted licenses with our free trial and clear interpretation. Then replace standing privilege with time-bound, policy-driven access and let lifecycle controls do the cleanup. The result: tighter identity control, with evidence to back every decision.