Compromised credentials are the wide-open gate into our digital estate
Credential compromise is the de facto initial access vector for breaches, accounting for roughly 22% of all incidents last year. More than any other entry point, with longer attacker dwell times that magnify damage and cost. In practice, attackers using stolen credentials remain in our environment for an estimated 300 days before we even detect them. [DeepStrike]
Breach detection alone isn’t enough. We need solid 24/7 protection and a repeatable, efficient, auditable way to scan for compromised credentials, and turn those findings into controlled outcomes. Not just tickets in a Jira backlog.
A Credential Siege
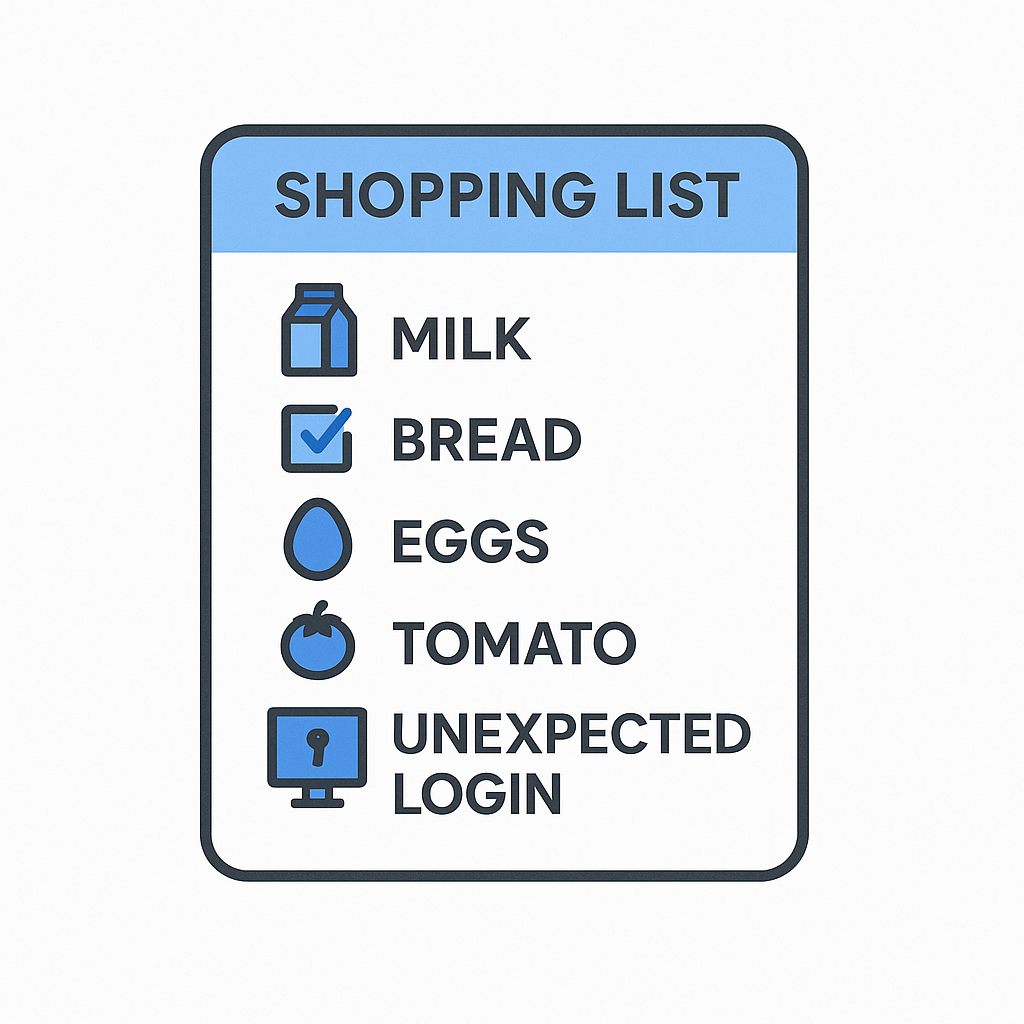
Compromised credentials aren’t just old passwords dumped on paste sites and (terrifyingly) available via dark web services. They include session tokens, long-lived API keys, service account and machine identity secrets, and anything that proves identity and carries privilege. Attackers leverage them for stealthier lateral movement, ransomware, and data exfiltration, most often without a noisy technical exploit.
Traditional detection efforts focus on finding leaked credentials or anomalous logins. Those are necessary, but not sufficient. What’s missing is a control plane that ensures that when a credential is risky, how that risk translates into damage is then minimal.
If compromised credentials are the problem, access governance and control are the solutions.
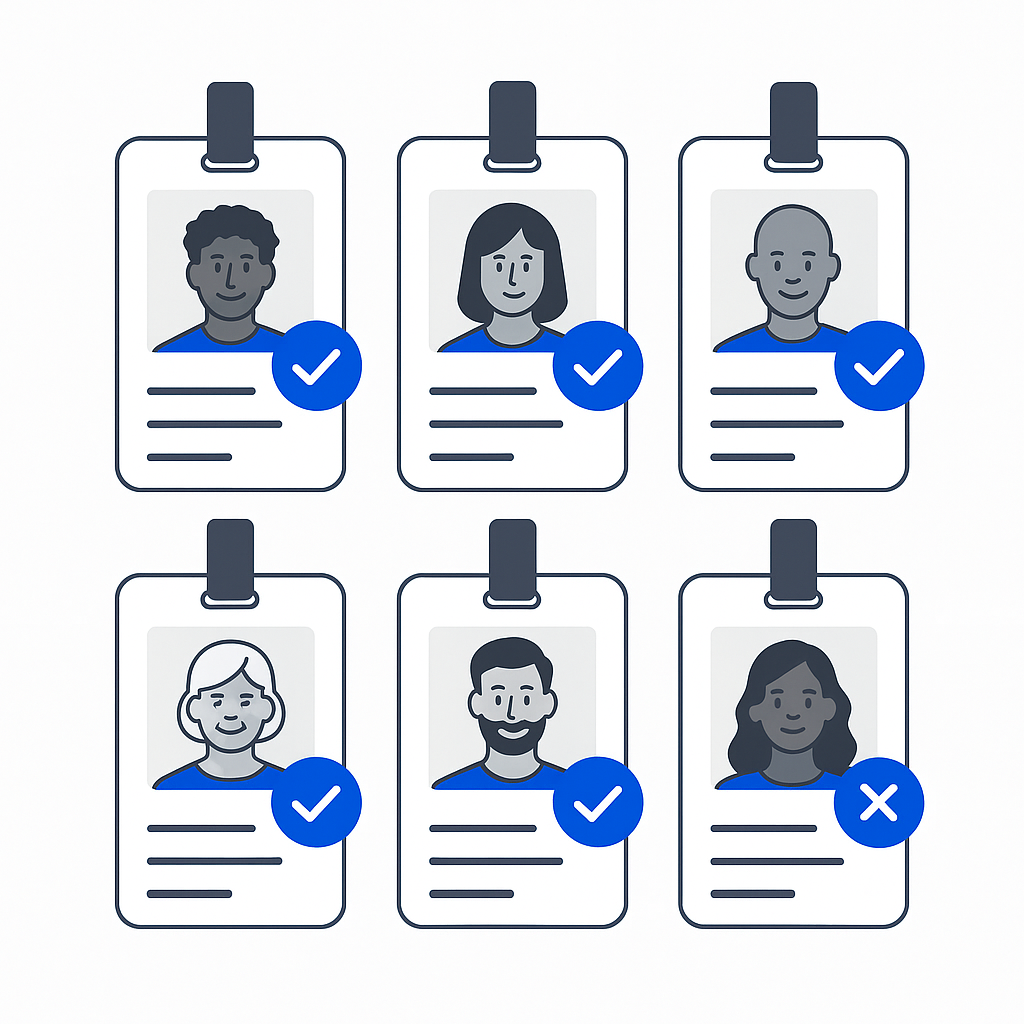
Step 1: Know What You’re Protecting
A scanning strategy fails if our inventory isn’t complete. We have to think beyond human usernames and passwords to include cloud provider access keys, API tokens and service account credentials, CI/CD pipeline secrets, and long-lived roles and delegated privileges.
Modern cloud-native environments are full of those “hidden” identities that attackers love. A leaked human credential is bad; an undetected or over-privileged machine identity is even worse.
Next, we need to integrate scans with breach data sources (even free ones) and internal logs to identify exposure early. Obviously we need to detect, and then we need to act.
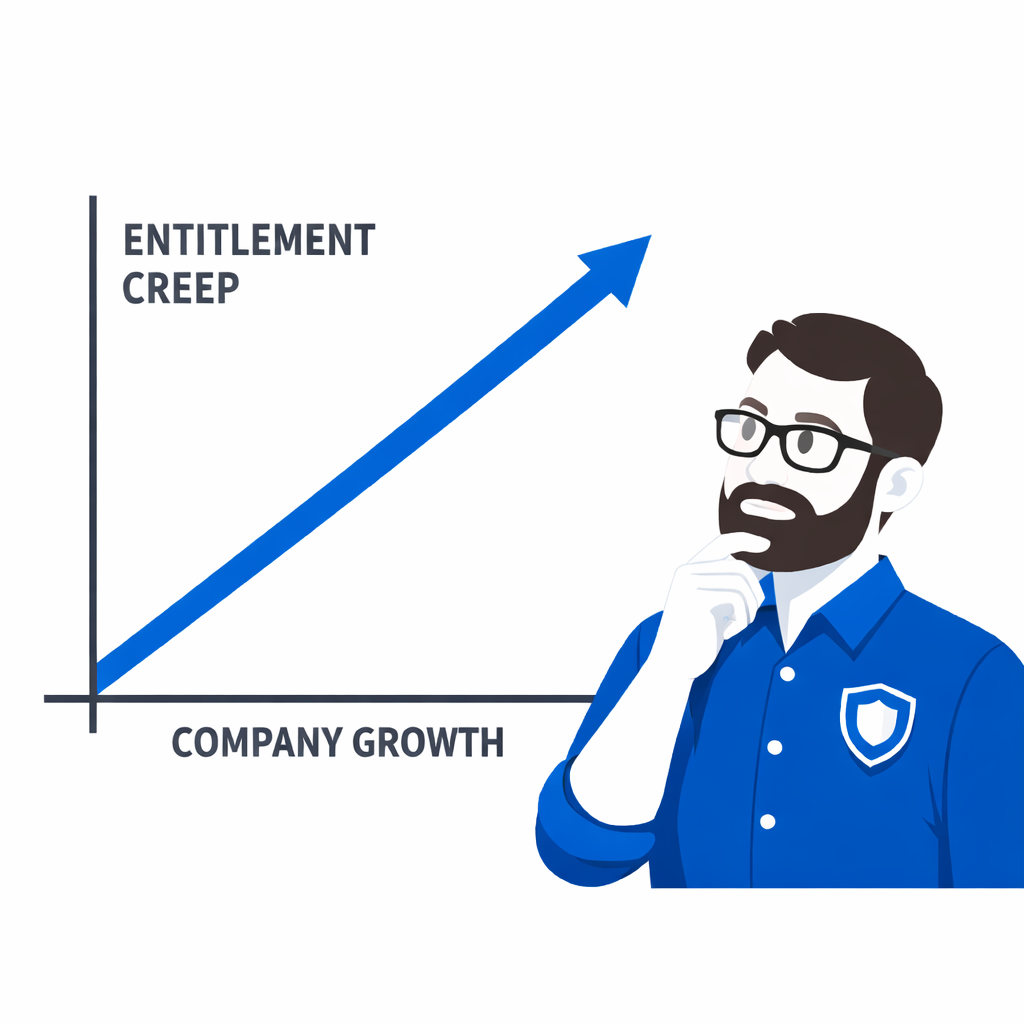
Step 2: Zero Standings: Just-Enough and Just-In-Time Access
Here’s where many programs hit a wall: we detect breached credentials but don’t remove their ability to do harm.
The cure is twofold: Remove standing access wherever possible and grant time-bounded access only when required.
This is just-in-time (JIT) access in practice. Instead of users sitting on permanent privileges, they request access for an individual task, a policy evaluates that request, and access is granted. But, only for the duration needed.
This approach turns compromised credentials into harmless noise. Even if an attacker obtains valid login details, there’s nothing of value standing around for them to misuse.
The broader security community underlines zero trust principles here: don’t implicitly trust a credential just because it checked out an hour ago. Authenticate and authorize per request.
Credential compromise is, alas, as inevitable as toast landing butter-side down. What’s not inevitable is giving attackers a free pass once we know about it.
Step 3: Signal to Response: Automated, Contextual, Auditable
Detection without remediation is just expensive logging. Scanning for compromised credentials should raise action signals that feed real-time decisions:
- Flag a risky identity
- Revoke risky entitlements or enforce stricter policies
- Trigger approvals for scoped replacements
- Audit everything automatically
For a busy security team, sophistication comes from automation and context. Imagine a leaked admin password is detected. The system can automatically:
- Reduce that admin’s entitlements to zero standing access.
- Require approval for any temporary higher privilege.
- Record every step in an auditable trail.
That’s where most traditional IAM tools stop; they alert but don’t act, and that’s why compromise dwell times remain stubbornly high.
Step 4: Treat Machine Identities With Respect
A lot of compromised credential discussions focus on usernames and passwords, but machine identities like service accounts, keys, even agentic AI, or tokens are often the main route to cloud assets.
It’s critical we discover all machine identities across cloud providers, apply least privilege for each. Wrap their access in controlled request-and-grant workflows, then expire any standing privileges automatically.
This is solid automation that dramatically reduces blast radius when credentials leak or are misused.
Step 5: Human Behavior Is Still a Clue
Credential compromises often present patterns:
- Credential stuffing
- Impossible travel
- Rapid repeated attempts
- Login from unfamiliar geographies
Our detection layer should feed these signals into our response engine. A well-tuned control plane can incorporate risk signals and map them directly to access changes without constantly involving the already busy help desk.
Practical Takeaways
Build pipelines that combine breach feeds, internal logs, and behaviour analytics.
- Control ruthlessly
Remove standing access, enforce JIT, get a tight grip on access creep, and apply zero standing privileges everywhere. - Respond quickly and audibly
Shift risky signals into automated enforcement. Revoke first, investigate second. - Audit to prove it
Metrics matter: mean time to revoke, mean time to remediate, % of identities with zero standing access, etc.
Making Credentials Useless
Compromised credentials aren’t the boogeyman at the edge of risk. They’re inside, and they’re the front door for most breaches. The smartest teams aren’t just scanning for them, they’re neutralizing their ability to matter.
In the modern identity-centric security model, we win not by preventing every compromise; we win by making sure credentials that are compromised are useless.