Snowflake data access shouldn’t have to be organizational theatre
Here’s a tale most security teams know only too well…
Marketing needs access to Snowflake to analyze lead generation metrics. Revenue ops wants pipeline data. Finance wants forecasting. Product wants usage analytics. Everyone agrees the data matters because Snowflake is now tied to decisions the business treats as oxygen: pipeline, revenue, planning, customer insight, and increasingly AI-driven analysis. Snowflake is doing its job. The access model around it is where the wheels get wobbly, and come off.
So marketing asks IT. IT points them to Data Engineering. Data Engineering says, “Easy, just run this SQL query.” To everyone outside that team, that may as well be carved on an obelisk in hieroglyphics. Now the request sits in a queue, the business waits, marketing stares at their screen like a dog that’s just been shown a card trick, engineers become human middleware, and security gets blamed for friction it didn’t actually design.
That is the Snowflake access problem in one scene: the business needs speed, data teams need control, and security needs least privilege, auditability, and something a bit more elegant than “Dave granted it on Thursday and meant to remove it later.” Snowflake security is not failing because the platform is weak. It is failing because too many organizations still operate access like a helpdesk pantomime instead of a policy-driven system.
Snowflake’s Power is Also its Complexity
Snowflake gives teams a reasonably flexible access model. Privileges are granted to roles, and roles are granted to users. From there, things get more nuanced: account roles, database roles, future grants, managed access schemas, row access policies, masking policies, secure views, ownership rules, and inherited permissions. That is all useful. It is also the reason casual access requests quickly become specialist work.
Managed access schemas are a good example. Snowflake recommends them because they centralize grant decisions and stop object owners from handing out access like sweets at a village fete. But centralization also means more dependence on a smaller set of admins or tightly held roles with MANAGE GRANTS. Great for governance. Less great when half the business is waiting on one or two people who speak fluent virtual warehouse.
This is why Snowflake security often becomes a translation issue. The requester thinks in terms of business need: “I need campaign attribution data for the quarterly review.” Snowflake thinks in terms of objects, roles, grants, policies, and scope. Somebody has to translate one into the other. In many companies, that somebody is a tired data engineer.
Why The Stakes Are Higher
The 2024 Snowflake customer compromise campaign made the identity side of this impossible to ignore. The campaign targeted Snowflake customer instances using stolen customer credentials, not a breach of Snowflake’s own environment. That matters because it shifts the debate. The danger is not just misconfiguration in the abstract. The danger is durable access combined with compromised credentials and weak hygiene around who has what.
Verizon’s 2025 DBIR found that 88% of breaches in the basic web application attack pattern involved stolen credentials. That’s not a niche edge case. That’s the main road. IBM’s 2025 Cost of a Data Breach report put the global average breach cost at about $4.44 million. Security teams don’t need another reminder that standing privilege is expensive; the bill keeps arriving anyway.
For Snowflake security, if users keep broad, long-lived access because removing it is awkward, then the organization is slowly converting convenience into attack surface.
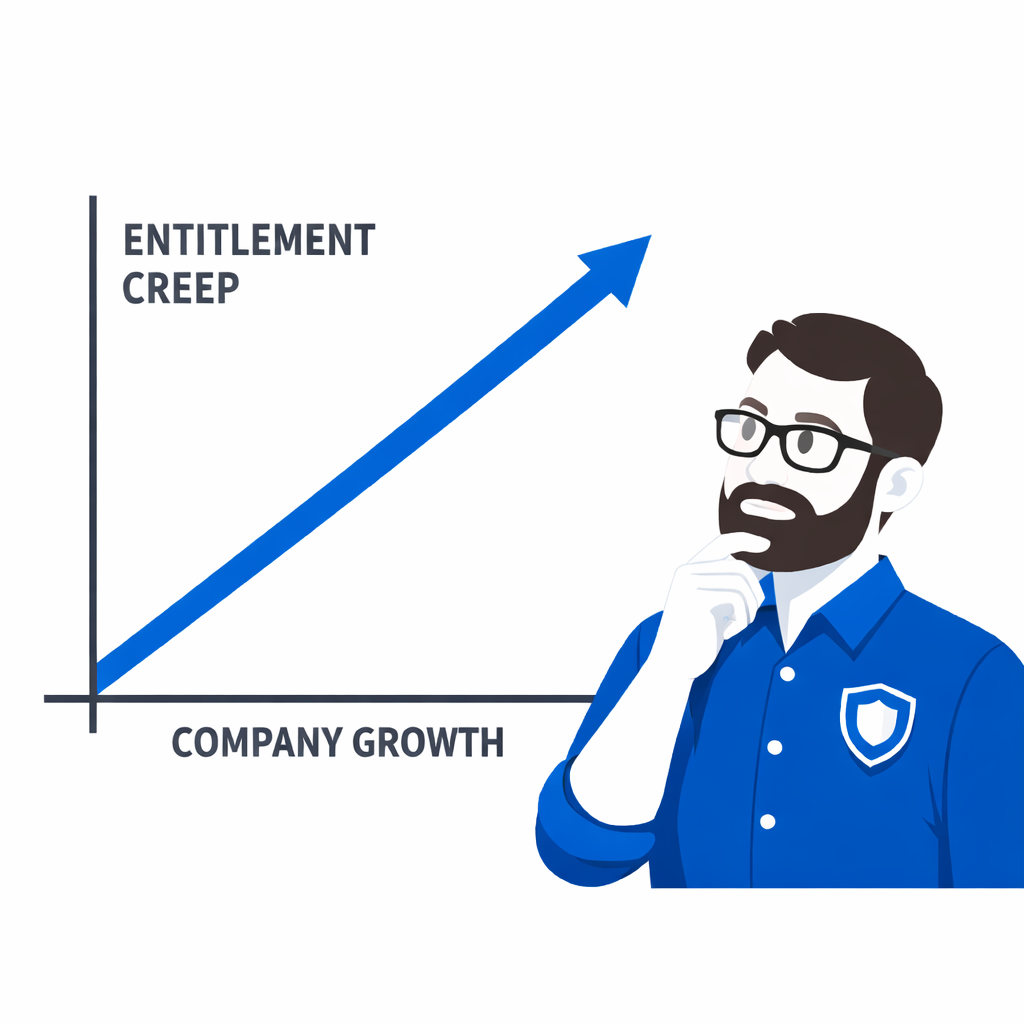
The Real Requirement is Frictionless Least Privilege
CISOs and information security engineers are under pressure from both directions. The business wants fast access to data. Regulators and auditors want evidence of least privilege, periodic review, and controlled privileged access. CISA’s Zero Trust Maturity Model explicitly points toward automated review and dynamic just-in-time, just-enough access for privileged requests. Snowflake security needs to meet that standard without turning every analytics request into a week-long pilgrimage.
That means the target operating model is not “more tickets, but tidier.” It is this:
A user requests access to the specific Snowflake role they need in Slack or Teams. Approval happens in-channel. Access is granted for a limited period. It is logged, reviewable, and automatically revoked when it expires. No console safari. No SQL handed to a marketer like a cryptic treasure map. No standing privilege left behind as a souvenir.
That is where we fit in.
How to Fix The Snowflake Access Problem
Our Snowflake integration is built around a very practical truth: most people who need access to data should not have to understand the mechanics of granting it. Instead of forcing users through SQL, tickets, or Snowflake workspaces, Trustle lets them request Snowflake access from Slack or Microsoft Teams, routes the approval to the right place with just in time provisioning, and then revokes it automatically when the approved access window ends.
That changes the shape of the whole process.
Business teams get self-service access without improvising around policy. Data Engineering stops being the unofficial translation bureau for every request. Security gets time-bound just-in-time access, audit-ready logs, and a cleaner path to zero standing privileges. Trustle also surfaces unused permissions and helps teams identify stale privilege that should not still be hanging around 90 days later like some troublesome house guest.
This matters operationally, not just philosophically. Cloud Security Alliance research in 2025 found that 58% of organizations struggle to enforce privileges, 54% lack lifecycle automation, and 46% struggle to monitor non-human identities. Snowflake doesn’t live in a vacuum; it sits inside a wider access estate already under strain. We give security teams a way to apply the same lifecycle discipline to Snowflake that they have been trying to impose elsewhere for years.
Snowflake Security is Also a Cost Story
Snowflake’s consumption model is brilliant until someone forgets that compute costs money every time curiosity hits “run.” Snowflake says suspended warehouses (the compute engines that run queries and process data) do not consume credits and recommends auto-suspend to control waste. Flexera’s 2025 State of the Cloud found organizations exceed cloud budgets by 17% and still estimate 27% of cloud spend is wasted. Broad access plus broad query freedom is not just a governance risk. It is a finance problem wearing an analytics badge.
Better Snowflake security means tighter access to the right data, through the right role, for the right time window. That reduces both security exposure and the odds of someone accidentally setting fire to the monthly compute bill.
The Better Model
The fix is not more heroics from IT or more patience from business teams. It is a control plane that makes secure access easier than insecure access. That is the part many organizations still lack.
Snowflake gives you strong primitives. We turn them into an operating model the rest of the company can actually use: request in Slack, approve in context, grant access just in time, review usage, revoke automatically, and keep the evidence when audit season arrives wearing its usual world-weary expression - check out our free no-obligation trial. That is what modern Snowflake security should look like. Not more waiting. Not more guesswork. Just faster data access with less lingering risk.