As a cybersecurity writer, for use in posts and blogs, I see and collate the latest cloud cybersecurity statistics and thinking from a variety of reputable sources. If you’re pulling together slide decks for C-level cloud entitlement management awareness, employee phishing training, or securing budgets for the next quarter, these recent reports make for compelling reading.
Identity’s still doing a lot of heavy lifting for attackers
1) Verizon analyzed 22,052 security incidents in its latest DBIR.
That’s a proper sample size, not just a handful of war stories. When a dataset is this large, we have to consider the patterns as operational signals, not just background chatter.
2) Of those, 12,195 were confirmed data breaches.
These findings aren’t just about attempted chaos, but successful harm. These trends (below) are tied to actual outcomes, not hypotheticals or near misses.
3) Credential abuse accounted for 22% of initial attack vectors in their 2025 DBIR.
Attackers still prefer logging in to breaking in, which is both old news and apparently still news. For defenders, that keeps identity hardening firmly in the “foundational control” bucket, not the “nice after the SIEM upgrade” bucket.
4) Third-party involvement in breaches doubled from 15% to 30%.
That’s the cloud-era trust problem in one unpleasant statistic. The modern attack path often runs through a supplier, contractor, SaaS platform, or partner integration before it reaches our estate.
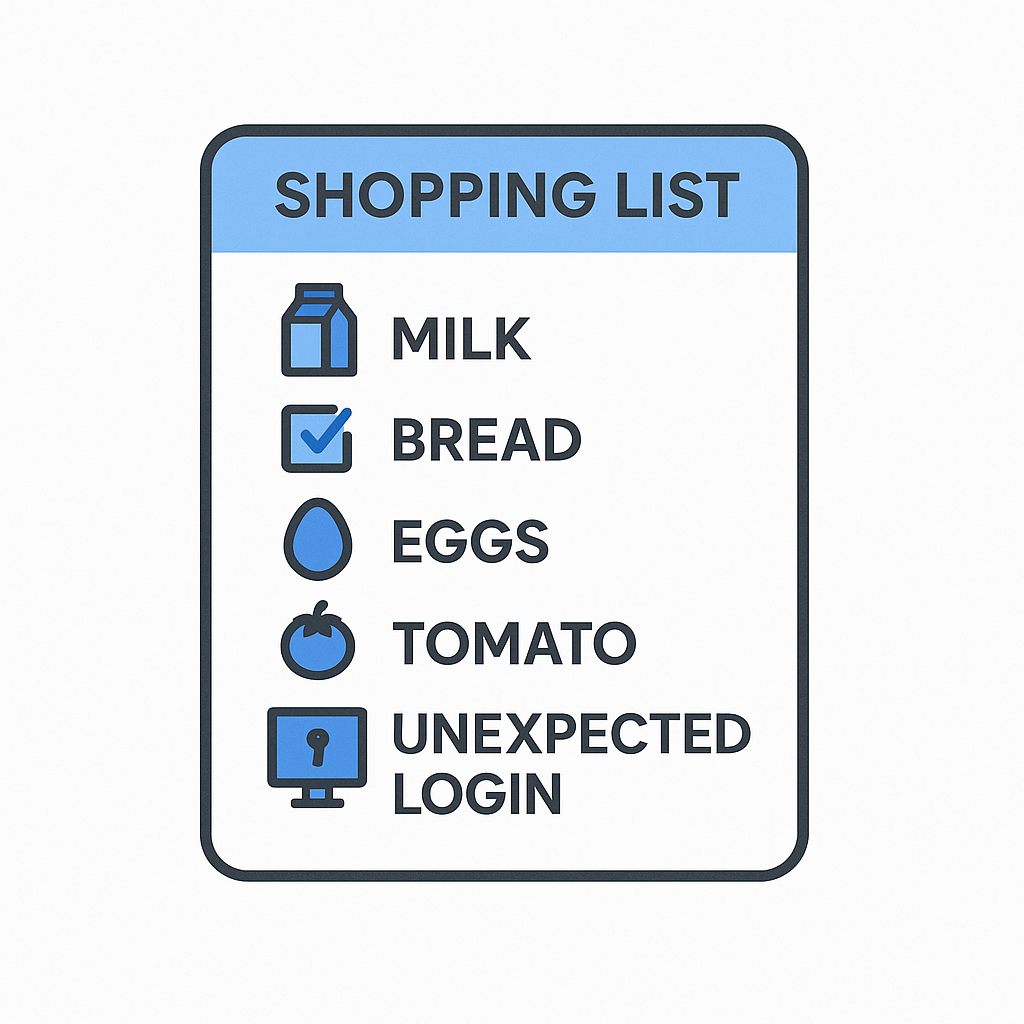
5) The median time to remediate leaked secrets found in GitHub repos was 94 days.
Ninety-four days isn’t a window; it’s a gaping hole. For SOC and cloud teams, it makes secret rotation and detection cadence look less like hygiene theatre and more like basic survival.
6) Microsoft says more than 97% of identity attacks are password spray or brute-force attacks.
So yes, the future includes AI, autonomous agents, and a whole lot of new acronyms. It also still includes criminals trying very obvious things at industrial scale, because obvious things keep working.
7) Modern MFA still reduces the risk of identity compromise by more than 99%, according to Microsoft.
That is one of the clearest “do the boring thing properly” statistics. Better authentication is necessary, even if it does nothing on its own to fix entitlement sprawl after an attacker gets in.
8) Microsoft says it thwarted 25.6 billion brute-force password attacks in the past year.
This is the sobering scale at which identity abuse now operates. If our controls still assume manual, occasional, human-speed attacks, we’re defending last decade’s problem.
9) Microsoft also blocked more than 35.7 billion phishing and other malicious emails.
Phishing’s still one of the cheapest dark web services to start an identity-led incident. For SOC teams, inbox protection and identity tracking controls are still joined at the hip.
10) Microsoft blocked more than 9.6 billion malware threats across its platforms.
Malware’s not gone away; identity abuse and malware now reinforce each other. Once access is compromised, malware, persistence, and lateral movement get a whole lot easier.
Multi-cloud has made access discipline much harder
11) 63% of organizations now use more than one cloud provider, according to CSA.
This is why access control consistency keeps falling apart in real life. Every extra cloud adds policy models, identity stores, roles, exceptions, and fresh opportunities for drift.
12) 82% maintain some form of hybrid infrastructure.
The fantasy of a neat, fully rational, single-plane control model can be retired with honors. Most security teams are still governing access across a messy estate of cloud, on-prem, SaaS, and inherited decisions nobody has fully documented.
13) 59% identified insecure identities and risky permissions as the top cloud security risk.
That is the headline number for this whole post. It tells CISOs that the market has largely stopped pretending cloud risk is mainly about perimeter thinking in nicer fonts.
Excessive privilege isn’t a theoretical problem
14) Among organizations with a cloud-related breach, 31% cited excessive permissions as a top cause. [CSA]
Overpowered identities turn small footholds into serious damage far faster. Least privilege no longer sounds like doctrine, it’s basic incident containment.
15) 27% cited inconsistent access controls as a top breach cause.
Security policy that changes shape between environments isn’t flexibility; it is ambiguity. Attackers adore ambiguity because it usually comes with attached forgotten privileges.
16) Another 27% cited weak identity hygiene.
CSA folds in unrotated keys, unused credentials, orphaned accounts, and missing MFA here, exactly the small operational sins that grow into major incidents. The word “hygiene” sounds gentle, but the consequences aren’t.
17) 33% still pointed to misconfigured cloud services or infrastructure.
Identity’s not the only problem, but it is the problem that increasingly combines with misconfiguration to produce the kind of day nobody wants.
18) 44% said implementing least privilege for identities is their top cloud security priority for the next 12 months.
That is encouraging, but also slightly revealing. Teams don’t elevate least privilege to top priority unless they’ve already been bitten by its absence.
19) Yet 42% still use MFA or SSO adoption as their main IAM KPI.
That’s useful, but it is also a bit like measuring whether the front door has a lock while ignoring who still has keys to the cellar, loft, and pantry. Mature programs need to measure privilege, anomaly, drift, and revocation, not just rely on login polish.
20) 28% cite lack of alignment between IAM and cloud security teams as a top challenge.
This is the organizational version of a misconfigured trust policy. If the teams managing identity and cloud posture are working from different maps, the estate will drift whether the tools are good or not.
21) 21% report difficulty enforcing least privilege at scale.
That’s not a reason to abandon least privilege; it’s the reason to operationalize it properly. Manual, ticket-heavy, exception-riddled models do not keep up with cloud change velocity.
22) 43% still emphasize incident frequency and severity over forward-looking risk reduction.
This is a classic reactive trap. If the dashboard only celebrates what went wrong, the program struggles to show the value of shrinking standing privilege before it becomes a headline.
AI is widening the access issue
23) CSA says 55% of organizations are using AI for active business needs.
AI’s no longer sitting in a sandbox making draft emails and odd pictures of hands. It’s moved into workflows, systems, and decisions, which means it is moving into our access model too.
24) 34% of organizations with AI workloads have already experienced an AI-related breach.
That should end the comforting idea that agentic AI security is still an early-adopter problem. The attack surface has already left the lab, burrowed into our SaaS tools, and joined production.
25) Only 26% conduct AI security testing.
That gap between adoption and assurance is the sort of thing that keeps incident responders employed. If a workload can touch data, systems, or tokens, it deserves testing and identity governance before implementation.
26) Just 22% classify and encrypt AI data.
That’s a control gap with consequences, especially where AI systems touch customer data, internal documents, or model inputs that could become tomorrow’s breach. Governance that stops at policy language isn’t governance; it’s stationery.
27) Only 15% implement MLOps security practices.
This is a clear sign that many AI programs are still operationally immature from a security standpoint. If model pipelines are running without the same effort applied to other production systems, risk accumulates fast.
Money, Zero Trust, and the numbers leaders can’t ignore
28) IBM puts the global average cost of a data breach at USD 4.4 million.
That gives the identity and privilege discussion a number that’ll raise our CFOs eyebrows. Excessive access isn’t just an architectural issue; it is a budget issue (and a very expensive one).
29) IBM says 97% of organizations reporting an AI-related security incident lacked proper AI access controls.
That’s as close as we get to a big neon sign saying “authorization still matters.” AI breaches are making headlines daily, and old access mistakes are becoming more dangerous when wrapped in automation and speed.
30) NIST’s 2025 Zero Trust practice guide documented 19 example ZTA implementations built with 24 collaborators.
Zero Trust has moved into practical implementation patterns. The excuse that this is all too abstract to do properly is getting flimsier by the quarter.
The through-line in these 2026 cybersecurity statistics isn’t subtle: cloud estates are getting more distributed, identities are getting less human, and excessive privilege is still where a bad day becomes a PR disaster.
In 2026, cloud risk is increasingly identity risk: too much access, too little context, too much drift, and not enough certainty about which human, workload, or AI-driven process is doing what. The blast radius now lives in permissions, stale secrets, shadow access, weak hygiene, fragmented ownership, and machine identities that nobody truly owns (until something catches fire). The winning move now isn’t more dashboards for their own sake, but tighter control over who can do what, for how long, and with enough evidence to prove least privilege at audit.